A) Peach
B) CeWL
C) OpenVAS
D) Shodan
F) A) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A company contracted a firm specializing in penetration testing to assess the security of a core business application. The company provided the firm with a copy of the Java bytecode. Which of the following steps must the firm take before it can run a static code analyzer?
A) Run the application through a dynamic code analyzer.
B) Employ a fuzzing utility.
C) Decompile the application.
D) Check memory allocations.
F) A) and B)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A client has requested an external network penetration test for compliance purposes. During discussion between the client and the penetration tester, the client expresses unwillingness to add the penetration tester's source IP addresses to the client's IPS whitelist for the duration of the test. Which of the following is the BEST argument as to why the penetration tester's source IP addresses should be whitelisted?
A) Whitelisting prevents a possible inadvertent DoS attack against the IPS and supporting log-monitoring systems.
B) Penetration testing of third-party IPS systems often requires additional documentation and authorizations; potentially delaying the time-sensitive test.
C) IPS whitelisting rules require frequent updates to stay current, constantly developing vulnerabilities and newly discovered weaknesses.
D) Testing should focus on the discovery of possible security issues across all in-scope systems, not on determining the relative effectiveness of active defenses such as an IPS.
F) A) and B)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A penetration tester is performing initial intelligence gathering on some remote hosts prior to conducting a vulnerability scan. The tester runs the following command: nmap -p 192.168.1.1, 192.168.1.2, 192.168.1.3 -sV -o --max-rate 2 192.168.1.130 Which of the following BEST describes why multiple IP addresses are specified?
A) The network is subnetted as a/25 or greater, and the tester needed to access hosts on two different subnets.
B) The tester is trying to perform a more stealthy scan by including several bogus addresses.
C) The scanning machine has several interfaces to balance the scan request across at the specified rate.
D) A discovery scan is run on the first set of addresses, whereas a deeper, more aggressive scan is run against the latter host.
F) B) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A penetration tester is scanning a network for SSH and has a list of provided targets. Which of the following Nmap commands should the tester use?
A) nmap -p 22 -iL targets
B) nmap -p 22 -sL targets
C) nmap -p 22 -oG targets
D) nmap -p 22 -oA targets
F) None of the above
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A penetration tester has obtained access to an IP network subnet that contains ICS equipment intercommunication. Which of the following attacks is MOST likely to succeed in creating a physical effect?
A) DNS cache poisoning
B) Record and replay
C) Supervisory server SMB
D) Blind SQL injection
F) A) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A client asks a penetration tester to add more addresses to a test currently in progress. Which of the following would define the target list?
A) Rules of engagement
B) Mater services agreement
C) Statement of work
D) End-user license agreement
F) B) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A company hires a penetration tester to determine if there are any vulnerabilities in its new VPN concentrator installation with an external IP of 100.170.60.5. Which of the following commands will test if the VPN is available?
A) fpipe.exe -1 8080 -r 80 100.170.60.5
B) ike-scan -A -t 1 --sourceip=apoof_ip 100.170.60.5
C) nmap -sS -A -f 100.170.60.5
D) nc 100.170.60.5 8080 /bin/sh
F) B) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A penetration tester executes the following commands: 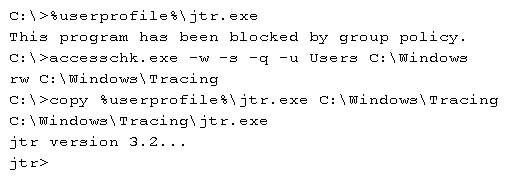 Which of the following is a local host vulnerability that the attacker is exploiting?
Which of the following is a local host vulnerability that the attacker is exploiting?
A) Insecure file permissions
B) Application whitelisting
C) Shell escape
D) Writable service
F) B) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A consultant is performing a social engineering attack against a client. The consultant was able to collect a number of usernames and passwords using a phishing campaign. The consultant is given credentials to log on to various employees email accounts. Given the findings, which of the following should the consultant recommend be implemented?
A) Strong password policy
B) Password encryption
C) Email system hardening
D) Two-factor authentication
F) A) and B)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A penetration tester is connected to a client's local network and wants to passively identify cleartext protocols and potentially sensitive data being communicated across the network. Which of the following is the BEST approach to take?
A) Run a network vulnerability scan.
B) Run a stress test.
C) Run an MITM attack.
D) Run a port scan.
F) A) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A penetration tester is performing a code review. Which of the following testing techniques is being performed?
A) Dynamic analysis
B) Fuzzing analysis
C) Static analysis
D) Run-time analysis
F) A) and B)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A penetration tester runs the following on a machine: 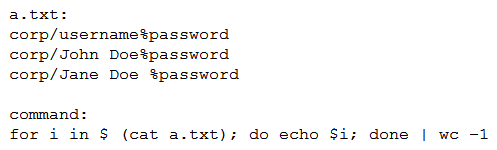 Which of the following will be returned?
Which of the following will be returned?
A) 1
B) 3
C) 5
D) 6
F) B) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Consumer-based IoT devices are often less secure than systems built for traditional desktop computers. Which of the following BEST describes the reasoning for this?
A) Manufacturers developing IoT devices are less concerned with security.
B) It is difficult for administrators to implement the same security standards across the board.
C) IoT systems often lack the hardware power required by more secure solutions.
D) Regulatory authorities often have lower security requirements for IoT systems.
F) None of the above
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A penetration tester used an ASP.NET web shell to gain access to a web application, which allowed the tester to pivot in the corporate network. Which of the following is the MOST important follow-up activity to complete after the tester delivers the report?
A) Removing shells
B) Obtaining client acceptance
C) Removing tester-created credentials
D) Documenting lessons learned
E) Presenting attestation of findings
G) None of the above
Correct Answer

verified
Correct Answer
verified
Multiple Choice
During a penetration test, a tester identifies traditional antivirus running on the exploited server. Which of the following techniques would BEST ensure persistence in a post-exploitation phase?
A) Shell binary placed in C:\windows\temp
B) Modified daemons
C) New user creation
D) Backdoored executables
F) A) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A penetration tester observes that several high-numbered ports are listening on a public web server. However, the system owner says the application only uses port 443. Which of the following would be BEST to recommend?
A) Transition the application to another port.
B) Filter port 443 to specific IP addresses.
C) Implement a web application firewall.
D) Disable unneeded services.
F) All of the above
Correct Answer

verified
Correct Answer
verified
Multiple Choice
While trying to maintain persistence on a Windows system with limited privileges, which of the following registry keys should the tester use?
A) HKEY_CLASSES_ROOT
B) HKEY_LOCAL_MACHINE
C) HKEY_CURRENT_USER
D) HKEY_CURRENT_CONFIG
F) B) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A penetration tester is performing initial intelligence gathering on some remote hosts prior to conducting a vulnerability scan. The tester runs the following command: nmap -D 192.168.1.1, 192.168.1.2, 192.168.1.3 -sV -o --max-rate 2 192.168.1.130 Which of the following BEST describes why multiple IP addresses are specified?
A) The network is subnetted as a/25 or greater, and the tester needed to access hosts on two different subnets.
B) The tester is trying to perform a more stealthy scan by including several bogus addresses.
C) The scanning machine has several interfaces to balance the scan request across at the specified rate.
D) A discovery scan is run on the first set of addresses, whereas a deeper, more aggressive scan is run against the latter host.
F) C) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Which of the following properties of the penetration testing engagement agreement will have the LARGEST impact on observing and testing production systems at their highest loads?
A) Creating a scope of the critical production systems
B) Setting a schedule of testing access times
C) Establishing a white-box testing engagement
D) Having management sign off on intrusive testing
F) A) and D)
Correct Answer

verified
Correct Answer
verified
Showing 61 - 80 of 165
Related Exams